Hello and Happy New Year!
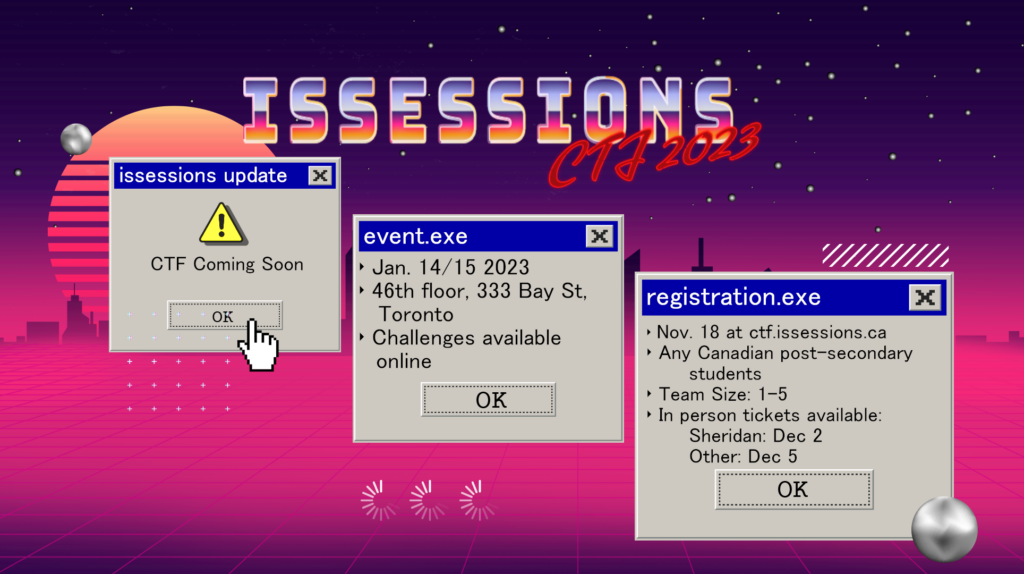
Next Thursday, January 12th, will be our first meeting of the year so don’t miss out! Jackson Gorny will be discussing his Declassified CTF Survival Guide, and we will be discussing a walkthrough on a few of our CTF Challenges in our upcoming CTF event. If you plan to attend the CTF this month, or any CTF, you won’t want to miss this meeting. See you then!
Meeting will be held in its usual location in person, room J102, and will also online here on discord and on our YouTube at https://www.youtube.com/@ISSessions
Agenda
Kick-Off 7:00
News 7:05
Jackson’s Declassified CTF Survival Guide 7:15
Break 7:30
CTF Challenge Walkthroughs 7:35
Jackson’s Declassified CTF Survival Guide
A rundown on each of the categories featured in this years CTF Tools for each category recommended by the developers themselves
CTF Challenge Walkthroughs
We’ll be taking three challenges from the actual CTF to go through Give your team a head-start on the competition